Part 3: Advanced Challenges and Cybersecurity
In the last part of our series, we looked at how websites manage high traffic and resource demands, drawing parallels with a busy restaurant. Now, we enter the more complex terrain of cybersecurity. Just as a restaurant might face unforeseen disruptions, websites too encounter unique challenges like DoS and DDoS attacks. Let’s explore these digital threats and the strategies to counter them, continuing our restaurant analogy for clearer understanding.
The Difference between Web Servers and a Website
Let's clarify the distinction between a “web server” and a “website.” In our analogy, consider the website name to be the same as the restaurant brand name "Gourmet Bytes," which boasts two physical branches situated side by side to accommodate a large number of patrons. In this case, we have one website (the brand identity) served by two separate premises (web servers). Patrons typically don't consider a restaurant's floor plan or its total area; they recognize it by its name. This same thing applies to the digital world as well — there are both modest and expansive websites, some of which rely on numerous web servers (like multiple restaurant locations) to manage high traffic and demand. This keeps the visitor focused on visiting the brand name (domain name) while hiding all the actual “brick and mortar” building details from the visitor.
Understanding Capacity Limits: When Restaurants Fill Up
The two dining areas, now efficiently managed by our savvy host (the load balancer), allow for a significant increase in capacity. But as with any space, there's a limit to just how many people it can hold.
On a particularly busy night, both dining areas become full. The host continues to greet customers and manage expectations, but now there's a queue forming again. Despite the increased capacity and efficient management, the reality is that resources are still finite – there are only so many tables, just as a web server only has so much bandwidth and processing power.
When both restaurants are at capacity, guests will again begin to experience delays. In the digital world, this is akin to what happens when there are server timeouts or slow loading times. At this point, even load balancing can't prevent the inevitable: if the demand exceeds supply, visitors will have to wait. You have probably encountered this on various websites in the past, where perhaps you were attempting to buy high-demand concert tickets, or purchase something on sale, competing with many other visitors; in these situations, a website can struggle to keep up with demand.
This analogy helps us appreciate that while load balancing is a powerful way to manage traffic and extend capacity, it's not an infinite solution. There comes a point when even the best systems reach their limit, and the restaurant – or website – must consider other strategies to accommodate growth.
Extending the Analogy to the Cloud
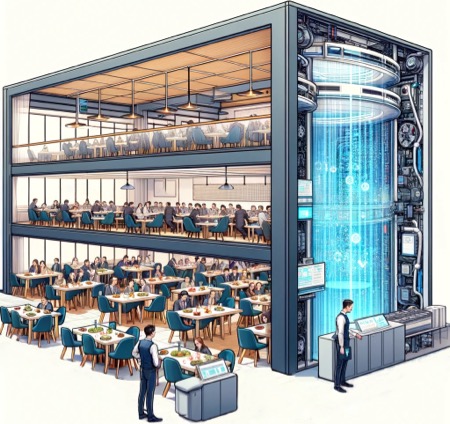
Cloud-hosted websites are akin to a dynamic restaurant that can instantly adjust its dining space to match the influx of customers. As an example, you arrive at the bustling "Gourmet Bytes" and it’s at full capacity. Instead of turning you away, or forcing you to wait, the host communicates with a third-party service that swiftly extends the height of the restaurant, adding more floors, tables, staff and resources as needed. As such, they can immediately seat you.
Later, as the rush hour wanes and diners depart, the floors contract, and the extra resources are removed. The beauty of this setup is that the restaurant — much like a cloud-hosted website — only incurs a charge for the additional square footage, tables and chairs, for the time they were actually in use, ensuring efficiency and cost-effectiveness tailored to real-time demand.
Denial of Service Attack (DoS)
Imagine one day that “Gourmet Bytes” suddenly becomes the target of a group harboring a grudge against the restaurant. This group orchestrates a “Denial of Service Attack” (DoS) with the goal of preventing “Gourmet Bytes” from providing services to its customers, resulting in loss of revenue, and loss of reputation.
How does this nefarious group do this? Well, they send people to flood the restaurant, taking up seats without any intention of ordering, effectively preventing genuine patrons from dining. Some members of the group exacerbate the chaos by ordering copious amounts of food and then walking out just as their orders are ready, leaving the kitchen overwhelmed and in disarray. This strategic onslaught of fake customers is designed not just to occupy space, but to cripple the restaurant's ability to operate effectively, reflecting the malicious intent of those who orchestrated it.
This situation at 'Gourmet Bytes' is similar to a Denial of Service attack on a website. Just like the restaurant, the website has finite resources. Here, the 'customers' are actually many malicious requests that flood the website and its web servers. They take up all the available connections and resources, preventing real visitors from accessing the content they are requesting.
Distributed Denial of Service Attack (DDoS)
Now, imagine if the problem of disruptive diners at 'Gourmet Bytes' wasn't just a local group of people but coordinated groups arriving in waves. These groups come from all over the city, and as soon as one batch is asked to leave, another group enters. This is not just a random occurrence; it's organized and relentless. The staff becomes so bogged down in handling these fake customers that the line outside grows longer, and real customers start to walk away, believing the restaurant is either too busy or has declined in service quality.

A “Distributed Denial of Service Attack ” (DDoS ) is like this scenario but operates on a much larger scale. Instead of a single source of malicious requests, the web servers are consumed by a flood of requests from many different locations and sources, which could be hacked computers or devices connected to the internet, from all over the world, at all times of the day. This orchestrated assault can completely overwhelm a website's resources, just like the restaurant's staff, making it nearly impossible to serve genuine visitors. The website, like the restaurant, becomes so busy dealing with these fake requests that it cannot fulfill its primary function.
Moreover, because the attack is distributed, it's harder to stop. Just like the restaurant staff might struggle to distinguish between a real customer and a fake one, a website has a tough time identifying legitimate traffic amidst the onslaught. The result is a crippling of normal operations, a tarnished reputation, and a frustrating experience for actual customers who can't access the website's services, just as real diners can't get a table at the restaurant.
Cloud Cost Vulnerability

In the cloud scenario, 'Gourmet Bytes' has an adaptive setup where additional dining space can be added to accommodate more guests during peak hours. This is a fantastic capability for a booming business, allowing them to serve more and more customers. However, during a Denial of Service attack, this flexibility turns into a vulnerability. The malicious crowd, which has no intention of eating, prompts the restaurant to expand continually; as a result, the restaurant incurs significant costs as they add more floors, tables, chairs, food, and staff to serve the influx of fake patrons.
The restaurant finds itself in a conundrum; it's forced to scale up due to the surge in apparent demand, but this expansion only leads to increased operational costs without any actual revenue, as these 'diners' neither order nor pay for any service. This scenario mirrors how a cloud-based website, designed to scale up during high traffic, can be financially burdened by a DoS attack that inflates its resource usage and costs, all while genuine users experience poor service or cannot access the website at all.
In the cloud, organizations can dynamically add resources and set caps on costs based on demand. But even with these safeguards, during a DDoS attack, all available resources will be consumed up to that cap. After reaching this threshold, resources become finite, leading to the website becoming unavailable.
Final Thoughts
As we've explored, the operational dynamics of websites, particularly in cloud environments, are intricate and subject to various challenges, like DDoS attacks. Understanding these complexities is crucial for businesses to effectively safeguard their digital assets and ensure uninterrupted service. While we've covered some fundamental aspects, this field is vast and constantly evolving. I encourage you to continue exploring and staying informed about the latest developments in cloud computing and cybersecurity to better navigate these digital waters.